
A new phishing technique called “file archiver in the browser” can be used by phishers to “emulate” a file archiver software in a web browser when a victim visits a .ZIP domain. The security researcher mr.d0x detailed the new attack technique.
In May 2023, Google launched eight new top-level domains (TLDs) that included .zip and .mov. Security experts are warning of malicious uses of these domains.
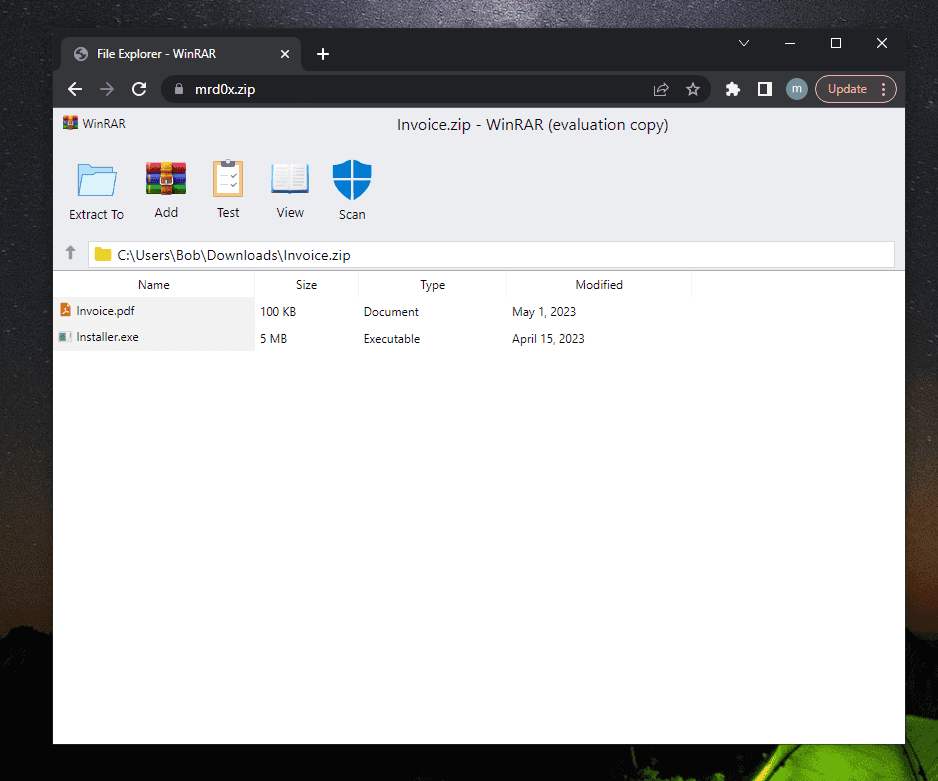
To carry out an attack using this technique, the attacker needs to emulate a file archive software through HTML/CSS. The researchers shared two samples, the first one emulates the WinRAR file archive utility, the second one the Windows 11 File Explorer window.
The researchers employed a clever trick, as depicted in the image below, where they added a ‘Scan’ icon to the WinRAR sample. When users click on the icon, a message box reassuring them that the files are secure is displayed, thereby preventing suspicion.
Then the researchers deployed the sample on a .zip domain that can be used for multiple attack scenarios such as:


The researcher noted that numerous Twitter users emphasized the Windows File Explorer search bar as an effective delivery method.
“Several people pointed out on Twitter that the Windows File Explorer search bar is a good delivery vector. If the user searches for mrd0x.zip and it doesn’t exist on the machine, it will automatically open it up in the browser. This is perfect for this scenario since the user would be expecting to see a ZIP file.” reads the analysis published by mr.d0x.
The recently launched TLDs provide attackers with more opportunities for phishing campaigns. The knowledge of this attack technique is essential to avoid beign victims of these attack.
It is strongly advised for organizations to implement blocking measures for .zip and .mov domains, as they are currently being exploited by phishers and are expected to see a further rise in their malicious usage.
“It’s highly recommended for organizations to block .zip and .mov domains as they are already being used for phishing and will likely only continue to be increasingly used.” concludes the expert.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, phishing)